A Guide on Better Security For Your Data & Personal Information
The Internet as the key to big change
In the last twenty years, the Internet has changed the way we communicate. This digital revolution has enabled us to provide a lot of information, services, entertainment, but also friends become available within cyberspace. With the internet, everything has become faster, more comfortable, and affordable. With the introduction of digitalization, service providers and policymakers become accessible with "two clicks". However, although the Internet has led to significant changes in quality of life, he also increased the risk of exclusion, because in this revolution they did not all categories of the population were equally involved.
Older women and men are at risk of being excluded, but more importantly to them due to digitalization, access to information and services will be denied, and therefore to them their human rights are denied. From a human rights perspective, this is certainly from one side a great challenge, but also an opportunity of our time.
How to protect yourself from identity theft?
Do not give your personal information over the phone, head to head, or via computer, if you are unsure if it's a verified person or organization. Never write down PINs for your payroll or credit cards on the cards themselves or any document or paper within the wallet. Get eliminate personal information in an exceedingly secure way (tear up paper, wipe/remove hard drives from computers before selling or throwing away). The number of documents you carry with you each day or leave within the car to a minimum. These are valuable items. Check the bank statements and statements There are unapproved card balance transactions. Report any discrepancies immediately or unauthorized activities to the bank or issuer cards. Be especially careful when leaving personal data on publicly available websites. Personal data may be misused in an exceeding number of the way by identity thieves searching websites.
What is SPAM?
Spam is sometimes considered unsolicited e-mail or unsolicited posts in thematic groups. In general, it's electronic mail sent to an inventory of addresses or to thematic groups during which some are advertised products. Spammers usually send an email to an inventory of 1,000,000 addresses and expect that only a tiny low number of readers will reply to their offer. Spams became one of the biggest problems for all internet users. Instead of posting an email address to the standard format, you'll be able to encrypt it additionally. To be an encrypted address email returned during a functional format, required is to be done by a careful and intelligent mind. The final thing you'll be able to resort to is that in the slightest degree do not share your email address. Make it temporary inboxes or forms through which they'll take you in direct contact. Users should prove that they're men by surfing the CAPTCHA test.
How to protect yourself?
Never enter your personal information on a website unless you are sure it is not fake. Check the website address carefully. If it resembles the URL of the actual business but is not the same, be careful. Never do visit your bank's website by clicking on the link - enter the website address yourself.
Do not provide your account information via phone, unless you have called and are sure that the number you called is not fake. If you call, look for a name and number so you can call later, when you check the number with when you receive a call matches the number for which you already know it's not fake.
Don't reply, don't click on links, and no open any files in spam messages. Do not call numbers from spam emails. Do not use software that fills in for you certain forms on your computer.
Never send your confidential information, accounts, or passwords in an email message. Email is a very insecure system. Check your bank statements and statements credit cards to make sure no one else does not have access to your account. Ask from the bank annual report on the use of credit cards to make sure no one is using Your name for raising money or hoarding debts.
Never lose sight of your card stores and refuse to slide the card through more than one machine. If you care about someone's store check behavior, contact your store supervisor or contact your bank.
Do not use ATMs that have suspicious devices attached to the hole for a card. Report something like that to the bank immediately.
Be careful when messaging in asking for your password, account information, and other data - even when the page is on the need to sign up looks right.
Carefully read what is written in small print letters in every offer you receive. If you received an offer by fax, and text not legible, ask for a better copy, but request send only if it is not a number with additional tariff.
Compare all invoices with purchase orders. You are looking for proof of purchase and check with colleagues to make sure you get what you paid for.
Why should you use Password Manager Software?
Using an identical password may be a major problem thanks to many website intrusions and stolen passwords, even on large pages. When your password leaks, malicious people have your email address, username, and password that they'll try on other sites. If you utilize identical login information, leaked information on one website may give others access to any or all of your accounts. If someone accesses your email account, they will also reset passwords on others, like bank orders. to forestall intrusions on other sites from being so harmful, you wish to use a distinct password everywhere. These should even be strong passwords - long, unpredictable words that contain numbers and symbols. the typical person has dozens of various passwords.
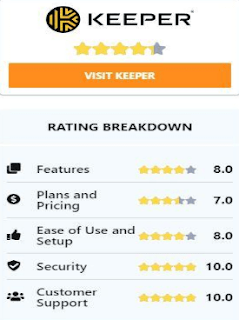
Remembering such strong passwords is sort of impossible without some trick. The best trick may be a password manager that generates secure, random passwords and remembers them so you do not need to. Password Managers like e.g. Keeper will relieve you of the burden, freeing your mind of remembering unnecessary password lists and allowing you to target something more productive.
After you use a password manager and want to log in to a website, you may first visit that site normally. Rather than entering the password directly on the page, you type the master password into the password manager, which automatically fills within the required fields on the page. (If you're already logged in to the password manager, re-entering the password is unnecessary).













Comments